(April 2011) AFTER DEPOSITING MY wallet, cell phone, parts of my uniform and various other sundries into the required plastic bins, I walked through the arch of the security magnetometer. I shuddered, fearing an activation of the chirping beep that would force me to succumb to a re-entry. I would then be required to remove the offending nickel or retractable pen from my pocket. But wait ... this particular country's procedures don't allow second tries. I would have to face the dreaded electronic wand.
When I passed through the gantlet without incident, it was a struggle to contain my relief. I sighed inwardly. Unfortunately, awaiting me on the other side of the X-ray belt was a terror far greater than I could have imagined. My steak sauce bottles were being scrutinized. “What?” you ask.
Yes, the prized steak sauce that I had purchased as a favor for a Florida neighbor was being examined by a 20-something equivalent of our Transportation Security Administration. I was being told that it was not acceptable to be brought on board the cockpit of the airplane that I was about to fly back to the United States — the same airplane that I would be operating as its designated captain.
Why? Because the plastic bottles that contained the steak sauce exceeded the 3-ounce limit by 1 ounce. Unscrewing a cap and showing the young gentleman that the bottles were sealed made no difference. It was just the rules, sir. Simple as that. With the bottles in my possession, I was a threat to crew and passengers. Certainly my command of a multithousand-pound jet was not nearly as consequential as a bottle of steak sauce. It made perfect sense.
If I wanted to transport the sauce home, my carry-on bag would have to be checked with the regular luggage. Rather than delay our departure, and for the sake of international security, I relented. How could I have been so cavalier?
In light of November’s passenger uproar regarding full-body scanners, perhaps it’s time to reflect upon the entire airline security process. Maybe the incident that I describe seems extreme. But consider the fact that the country utilizing these procedures is the closest ally of the United States. And consider the fact that the procedure is adhered to at checkpoints designated specifically for crew members and airport personnel. Crew members transiting regular passenger security screening in the terminal apparently are not treated to such indignities. Almost 10 years after 9/11, are we appropriately addressing the risk?
In so many words, I posed this question to aviation security expert Tom Walsh. Tom is a 767 captain for a competing major carrier. His resume in the security arena extends beyond the scope of this column. Suffice it to say, he is highly qualified and respected within the industry by both his peers and law enforcement. His opinions and perspective are utilized by one of the consulting firms that advise the TSA through Homeland Security Presidential Directive 16, the U.S. National Aviation Security Strategy.
Interestingly enough, the TSA seems to take advice better from professionally paid organizations than from advocacy groups such as pilots unions. Granted, certain U.S. policies restrict the consultation that can be obtained through labor groups, but it seems ironic that a pilot wearing a different hat becomes more credible when he is employed by another industry. The unfortunate part of the irony is that the U.S. taxpayer is indirectly paying for Tom’s expertise.
This is not to say that the TSA isn’t listening. On the contrary. Tom’s consulting firm assesses the risk of a terrorist threat through a formula that involves vulnerability, capability, enemy intentions and the appropriate consequences.
What can we do better to mitigate the risk of terrorism aboard U.S. airlines? The single most important strategy is to change our philosophy about the screening process. In the United States, we focus a major portion of our energies on discovering the instrument of the threat rather than the individual who has the intent to carry out the threat. Passengers are treated equally as though everyone is a potential terrorist. It wastes time and resources. What philosophy might be more efficient?
First, consider the Israeli attitude that intelligence gathering is the single most important counterterrorist tool. Remember Richard Reid of shoe bomber fame? He attempted an operational test aboard an El Al flight and determined that the risk was too great. The Israelis already had a file started on him. He didn’t operate in a vacuum. He was a bona fide operative of al-Qaida. And so was his partner. But Reid’s partner got cold feet the day before the incident. The partner is resting comfortably in a U.K. prison cell.
How about the Nigerian underwear bomber from Christmas Day 2009? Do you think that his intentions were not part of a larger scheme? Although his almost comical efforts should place him on the Darwin Award list, the underwear bomber’s involvement can be traced back to a radical Muslim cleric in Yemen — the same cleric who provided us with the printer cartridge bombs found aboard two cargo airplanes back in October. All of this information was obtained with the use of good intelligence-gathering tools. Tom has no doubt that the Israelis would have prevented the young Nigerian from ever boarding an airplane.
Another shift in screening philosophy would be to redefine the ugly word profiling. Tom Walsh said profiling is not about race distinctions but rather the science of detecting behavior patterns that indicate a threat potential. This behavior detection is a well-known science. But it requires adequate training. This training not only has to extend to TSA employees but to airline agents, crew members and ground personnel as well.
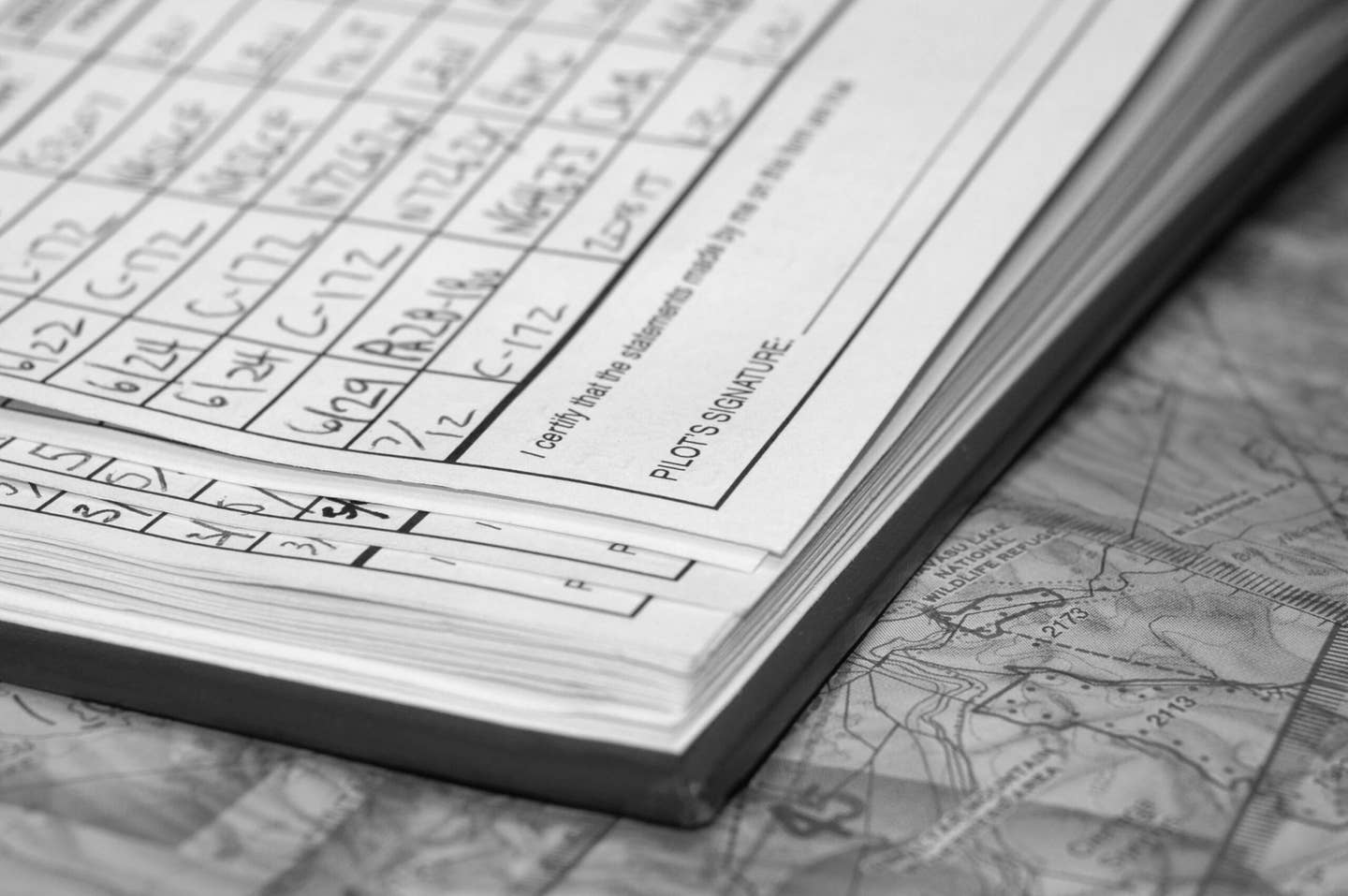
To assist in reducing the number of passengers screened via behavior detection, filter out the least likely terrorist potentials. For example, crew members who have been adequately screened and documented are not a threat. Most of the documentation infrastructure is already in place for pilots. The documentation is currently used for interline jumpseat privileges. The technology of biometrics (fingerprints, retinal scans, etc.) could be employed for further identity confirmation. The gazillion dollars appropriated for support of the contentious body scanners could be applied toward finalizing a secure system for crew-member access at a fraction of the cost.
Body scanner technology does not have to be eliminated. The technology can be effective if it is employed in a private setting with individuals who don’t pass the behavior analysis test. And, yes, some passengers will be subjected to the process unnecessarily. No system is perfect.
Further promote the Trusted Traveler Program as another example of utilizing security resources appropriately. Why subject the business people who are frequent users and premium revenue sources for the nation’s airlines to the same barrage of screening procedures? If they volunteer for background check verification, can’t we eliminate them from the threat list?
How effective are the FFDO (federal flight deck officer) and air marshal programs? For various reasons that fall under the heading of sensitive security information and can’t be discussed publicly, Tom considers these programs to be “strategic deterrents” rather than ultimate terrorist elimination tools. Combined with other tools, FFDOs and air marshals are useful layers of the security process. But if the bad guys have already initiated their evil plan on board the airplane, wouldn’t a secondary barrier for the cockpit door slow down the process … if not thwart entry completely? Perhaps we should focus some of our security resources in that direction. The Israelis have been flying for years with a double cockpit-door system.
Tom reminded me that successful terrorist plots have consistent patterns. The plots are tested in the field. The plots usually involve multiple targets simultaneously. Terrorists frequently return to the challenge of attacking a missed target. And aviation is still a desirable target.
Both Tom and I enjoy flying general aviation airplanes. How does the TSA view the threat to GA? Will we be facing a body scanner and/or magnetometer at the next EAA AirVenture?
The government considers a small airplane both ammunition and a transport vehicle. Depending upon the speed and fuel capacity, the TSA perception is that a GA airplane has the potential to create havoc at places like power plants or sports events if used as a guided missile. A corporate jet could be chartered internationally to transport a weapon of mass destruction. These are not new revelations.
Although it seems that the TSA will relent on formal screening procedures for airplanes above 12,500 pounds by increasing the gross weight limit, we little airplane guys are still at risk of losing freedoms we have taken for granted. What can we do?
Simple stuff. Lock the prop. Lock the airplane doors. Lock the hangar. Lock entry gates. Designate a security coordinator at your home airport. Form an informal pilot community with a membership list that allows for easy identification of a suspicious outsider. One example of a successful GA security program utilizes nonpilot aviation enthusiasts. These enthusiasts log N-numbers of airplane takeoffs and landings. This familiarity can assist in questionable operations at the local airport. If these techniques are instituted on our own initiative through advocacy groups like AOPA, perhaps the TSA will move on to greater threats.
Regardless, it is time for all of us as pilots and passengers to re-evaluate the priorities that our government has determined are in our best security interests. If an airline pilot’s steak sauce is considered a threat, are we moving in the right direction?

Subscribe to Our Newsletter
Get the latest FLYING stories delivered directly to your inbox